Advanced App Development Techniques
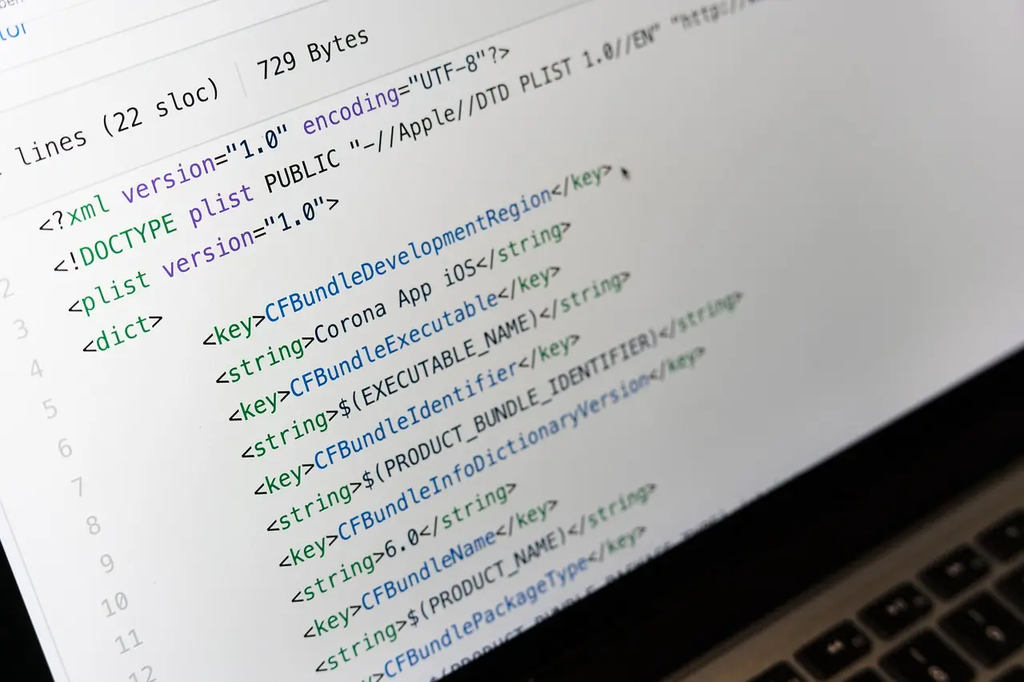
Advanced App Development Techniques (Daily Mobile Apps) refers to sophisticated methods and strategies used to create high-quality, efficient, and user-friendly mobile applications. These techniques may include utilizing cutting-edge frameworks, optimizing app performance, implementing robust security measures, and integrating innovative features such as machine learning or real-time data processing. By applying these advanced practices, developers can enhance user experience, ensure app reliability, and stay competitive in the rapidly evolving mobile app industry.
Advanced App Development Techniques
Advanced App Development Techniques (Daily Mobile Apps) refers to sophisticated methods and strategies used to create high-quality, efficient, and user-friendly mobile applications. These techniques may include utilizing cutting-edge frameworks, optimizing app performance, implementing robust security measures, and integrating innovative features such as machine learning or real-time data processing. By applying these advanced practices, developers can enhance user experience, ensure app reliability, and stay competitive in the rapidly evolving mobile app industry.
💡 Key Takeaways
- Apply advanced architectural patterns (e.g., Clean Architecture) for scalable, maintainable apps.
- Optimize performance with efficient state management, lazy loading, and profiling.
- Implement comprehensive testing (unit, integration, and UI) across platforms.
- Build secure and accessible apps with strong authentication and inclusive UI practices.
- Automate builds, tests, and deployments with modern CI/CD workflows.
❓ Frequently Asked Questions
What is MVVM (Model-View-ViewModel) and when should you use it?
MVVM is a UI architecture that separates data (Model), UI (View), and presentation logic (ViewModel). It improves testability and maintainability, and is especially helpful for complex, data-driven interfaces with data binding.
What are common techniques to optimize app performance?
Profile to find bottlenecks; minimize main-thread work and overdraw; implement lazy loading, paging, and image caching; offload heavy tasks to background threads; use efficient data structures and asynchronous APIs.
What is CI/CD and why is it important for app development?
Continuous Integration/Delivery automates building, testing, and deploying apps, catching issues early, enabling faster, more reliable releases, and ensuring consistent environments.
What are essential security practices for mobile apps?
Encrypt sensitive data at rest, use secure network communication (TLS, certificate pinning), validate inputs, avoid hard-coded secrets, apply code signing/obfuscation, and enforce least-privilege access to APIs.
